In early July, IT solutions provider and remote management solution provider Kaseya announced that it had fallen victim to a supply chain ransomware attack. During the attack, hackers leveraged a vulnerability in Kaseya’s VSA platform to encrypt the data of hundreds of downstream MSPs and their clients.
The Kaseya ransomware outbreak is one of the latest high-profile ransomware attacks targeting enterprises. With the average cost of remediating a ransomware attack reaching $1.85 million in 2021, the financial impact of this attack could be devastating to the victims.
This article will look at what happened during the Kaseya ransomware breach in detail. It will also outline how security leaders and users can protect themselves from other ransomware threats in the future.
The Kaseya Ransomware Attack: Here’s What Happened
On July 2nd at 2 pm EST, Kaseya was alerted to a ransomware attack on internal and external sources. They responded by shutting down internal systems and advised customers to disconnect VSA servers.
During the attack, the hackers encrypted the compromised data and demanded a ransom of $70 million in bitcoin in exchange for a decryption key that would unlock the encrypted systems. So far, the ransom hasn’t been paid, meaning that many of the affected MSPs are still unable to access their data.
While Kaseya responded quickly, the attack affected close to 60 Kaseya clients, many of them MSPs managing the IT systems of small businesses, leading to the hackers compromising around 800-1500 downstream small businesses.
How the attackers managed to gain access to the system remains unknown. What is known is that the group behind the attack is a Russian-speaking cyber gang called REvil, which has disappeared. As Security Researcher Lawrence Abrams notes, “All REvil sites are down, including the payment sites and data leak site.”
7 Ways that Security Awareness Leaders Can Prevent Ransomware Attacks
The Kaseya ransomware attack highlights that these types of attacks are becoming more complex. The incident also reaffirms that security leaders need to be proactive to keep cyber criminals at bay. Below are seven ways for security leaders to prevent ransomware attacks:
1. Educate your employees
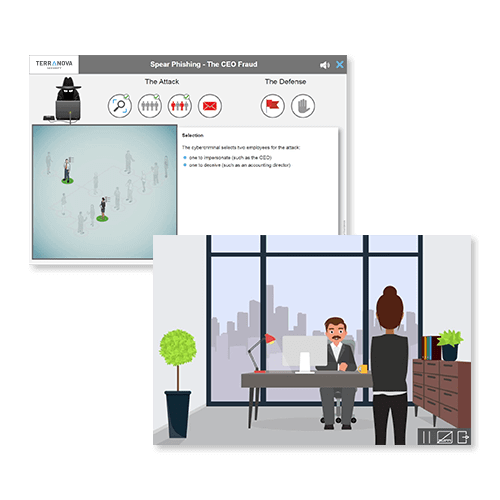
Use real-life scenario-based training to teach your employees how and when to open attachments from senders they don't know. Engaging training can include gamification, microlearning, simulations, animated videos, and interactive online training.
2. Develop Cyber Security Heroes
Focus on building a culture that encourages employees to make behavior changes and develop internal cyber security heroes to motivate other employees to keep your organization safe and secure.
3. Communicate Regularly
Provide employees with ongoing communications and campaigns that educate them about the latest ransomware threats and the risks that come with opening emails, text messages, attachments, and connecting foreign USB drives.
4. Configure your anti-spam filters for dangerous file types
Many cyber criminals use common executable file types to launch ransomware attacks, so encouraging employees to set spam filters to flag files like .exe, .vbs, and .scr can or preventing the activation of macros in productivity software help prevent malicious files from making it through your defenses.
5. Employ the Principle of Least Privilege
Ensure all your users only have the level of access to the systems and data needed to do their job. That way, if their device gets infected with ransomware, then only some of your organization's data will be compromised.
6. Monitoring your Network
Monitoring your network with tools like network monitoring platforms and SIEM software will help you to identify malicious activity and catch ransomware attacks early before they can cause catastrophic damage to your organization.
7. Maintain and protect your systems
Maintain your operating systems and software to the latest versions and with the latest patches. Employ a backup strategy and architecture that defends against ransomware and allows for a quick recovery.
How to Protect Your Data from Ransomware Attacks: Tips for End Users
End users are your organization’s first line of defense against ransomware threats, and security awareness is their best weapon against skilled attackers. Below are some steps users can take to protect their data from ransomware attacks:
1. Inspect website URLs in messages
Check all emails for fake URLs that contain suspicious elements like changed or additional characters and misspellings of common words, as these could indicate that the sender is trying to manipulate you into visiting a phishing site.
2. Never click on unverified or suspicious links
Never click on email links from unknown senders or links that lead to an unfamiliar website, as these can automatically start downloading malware that puts your personal information at risk.
3. Don’t open email attachments from unknown senders
Opening email attachments is one of the most common ways users' devices get infected with malware, so never open email attachments that don't come from a trusted sender.
4. Avoid using unfamiliar or unauthorized storage drives
Don't use any foreign physical storage media, like USB flash drives or backup hard drives, as these can infect your device with malware. It's not uncommon for cyber criminals to leave these devices in public places to trick employees into using them.
5. Regularly scan and update your system software
Do not interrupt antivirus scans and update your software when prompted to ensure that your device is secure and up-to-date with the latest security patches. Keeping your devices patched will eliminate vulnerabilities that attackers can exploit.
6. Protect Your Files
Store your files in authorized locations where they are periodically backed up to ensure that you have copies of your files if your files are lost or encrypted during a ransomware attack or security incident.
7. Report Incidents
If you suspect a ransomware infection, do not contact the hackers or pay the ransom. Report it immediately to the IT support department according to organizational procedures.
Recap
Ransomware attacks are a pervasive threat to modern enterprises because they are easy to pull off. All it takes for a hacker to launch an attack is to trick an employee into clicking on a malicious email attachment that starts installing malware. The most effective way to address these threats is with proactive security awareness training.
Security awareness training and phishing simulations will teach employees how to spot dangerous emails and help them to avoid clicking on malicious links and attachments. This investment will reduce the likelihood of a ransomware outbreak and give your employees some assurance that they can work safely.
Want to train your team to detect malicious email attachments?
Instill a security awareness culture within your organization, contact us today!