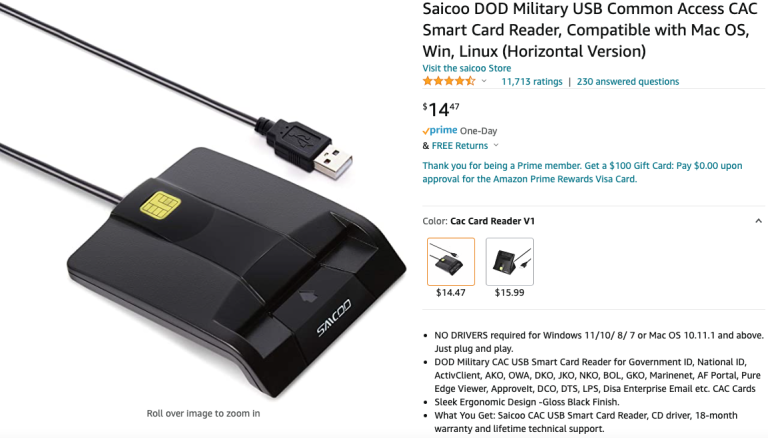
KrebsOnSecurity blog recently reported on a popular, low-cost Common Access Card (CAC) reader available on Amazon that came with drivers infected by malware.
A compromised smart ID card reader can bring severe consequences to both government and private organizations. It gives hackers an easy backdoor means of infiltrating networks and systems, which can leave sensitive information vulnerable to a leak or data breach.
This report is particularly concerning since CACs are the standard card used to grant physical access to buildings, controlled spaces, and Department of Defence (DoD) networks and systems. Many active-duty personnel and defense contractors have purchased this device for home and remote use.
Because of the technology’s ubiquity, not to mention the increased prevalence of malware attacks worldwide, organizations must educate their employees on the potential dangers inherent in smart ID card readers, as well as how they can detect and avoid possible threats.
How Does Malware Get on Smart ID Readers?
In the case highlighted by the KrebsOnSecurity blog, when a low-cost card reader purchased on Amazon wouldn’t work right out of the box, the purchaser went to the manufacturer’s website to download a ZIP file of updated driver files.
Scanning the drivers with online virus checkers revealed the presence of the Ramnit malware, an older threat still used in sophisticated data exfiltration attacks.
While buying a smart ID reader that comes bundled with malware is (hopefully) unusual, this case shows even brand-new hardware is vulnerable to being infected out of the box. Manufacturer websites can get hacked and malicious downloads inserted in the place of the original legitimate ones.
Always be cautious when downloading and installing updates for card readers, particularly if they don’t appear to come directly from the manufacturer or your organization. Be cautious, report anything suspicious to your IT team, and if in doubt, verify updates with a phone call or email to the manufacturer.
Dangers of Smart ID Card Readers Infected with Malware
As a popular, low-cost option on Amazon, countless federal employees and military personnel have potentially bought this exact reader to enable them to access email and networks from home. Some security experts argue the reported attack likely targeted defense workers due to the hardware’s popularity.
Any company that relies on similar security cards and ID scanners and does not supply its staff with trusted, vetted card readers for remote use is leaving itself vulnerable to breaches.
The security threats posed by many new, increasingly distributed work environments have become well-known over the last several years. Given the rise in malware and ransomware attacks, all organizations and employees must be vigilant to avoid letting malicious actors access their systems.
Examples of Common Malware Threats
While there are various kinds of malware, they should all be considered serious threats as each can have a lasting impact on sensitive information and devices.
Software that silently monitors activity and logs keystrokes poses the most severe risk. It records sensitive information, such as credit card information and login details, or sets the stage for industrial espionage.
Disruption of an organization’s operations is another malware-related threat. This type of attack can inject ransomware into a device or network, locking and encrypting files until the victim pays the ransom. Cyber criminals usually ask to get paid in cryptocurrency. However, even if a ransom is paid, obtaining access to sensitive information held hostage is never guaranteed.
And malware can also be used for command-and-control attacks. In these attacks, the malware uses a computer’s processing power to conduct other illegal activities such as cyber attacks, selling illicit goods, hosting illegal files, or even mining cryptocurrency—usually without a user noticing.
Leveraging Security Awareness Training to Defend Against Malware
The best kind of malware protection is detection and prevention. These precautions can be achieved primarily via implementing good cyber security guidelines and effective security awareness training for your users to reduce the risk associated with malware attacks. These 10 simple steps can help you improve your cyber security posture:
- Raise security awareness in your organization.Deliver information security awareness to all employees regularly to inform them how to prevent malware infections and what to do if they detect a compromised system.
- Run regular phishing simulations. This exercise allows you to identify potential vulnerabilities before they may be exploited and is a great teaching opportunity for your users.
- Keep your antivirus up to date.This type of software is only as good as its database of malware signatures it can compare files to, so ensure you have automatic updates enabled.
- Keep systems and applications up to date. Operating systems and software should always run the latest version to ensure all patches are installed.
- Only use legitimate software apps.Only download and install software on company computers and servers based on a pre-approved list.
- Put a mobile device policy in place. Don't allow users to connect their mobile devices to their work machines. Many forms of malware can be transmitted from mobile to desktop via a USB connection.
- Identify external emails. These usually display an EXTERNAL tag next to emails from outside your organization and serve as a visual reminder to ensure your users are extra vigilant with potential file downloads.
- Limit administrative privileges. This precaution helps prevent the accidental disablement of security controls or the installation of unwanted software.
- Backup electronic data. The best protection against ransomware is a solid backup strategy with ransomware protection capabilities.
- Secure file sharing. Limit the locations and services users can use to download files. Free and public file-sharing services may host malware disguised as other files.
Strengthen Your Organization's Cyber Security Awareness Culture
Some low-cost, commercially available security ID card readers have recently been shown to pose a malware threat to your business. Users should rely on trusted devices and be cautious when downloading updates for card readers.
Given the threat posed by malware, the first line of defense should always be an aware, well-trained staff who can spot threats to your systems and networks.
Effective security awareness training equips employees with the knowledge to spot warning signs, report suspicious activity, and protect sensitive systems.

Cyber Security Hub: Access Exclusive Cyber Security Content
Feel free to visit our free Cyber Security Hub to find shareable crucial information about malware, phishing, and other cyber threats.