“On the internet, nobody knows you’re a dog.”
There’s a reason Peter Steiner's cartoon gained popularity in 1993 and has now become an iconic representation of how the internet works.
The internet provides a way for people to hide their real identities, which can unfortunately lead to dishonest activities. Nowadays, scammers take advantage of this to deceive people who either trust too easily or are just unaware.
Many bad actors use a cyber attack technique called spoofing to trick people into divulging sensitive information. In a spoofing attack, the bad actor often poses as a well-known company or brand and sometimes even uses forged email headers that look legitimate. The attack usually starts with phishing emails containing fraudulent links. However, many hackers go one step further and design websites that impersonate the brand. They might even register the domain, so the site seems perfectly legit at a glance.
With the rapid growth of online shopping, this practice is rising. In just the first half of 2023, the average brand was targeted by 39.4 look-alike domains per month, according to Fortra's 2023 Domain Impersonation Report.
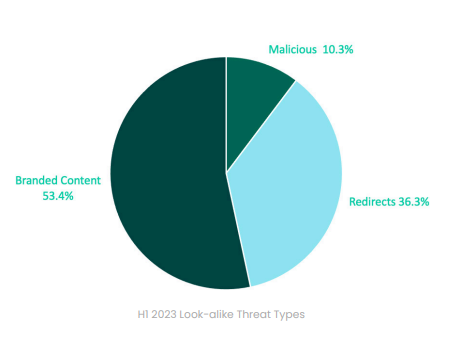
Source: Fortra
The report also discovered that 53.4% of look-alike domains hosted branded content. Let's look at the world’s five most spoofed companies below and get tips on how to avoid spoofing attacks.
These 5 Brands are the Most Spoofed in the World
According to a recent report by cyber security firm Check Point Research (CPR), these are the top 5 spoofed brands in the third quarter of 2023:
- Walmart
- Microsoft
- Wells Fargo
- Amazon
For many observers, it was a surprise to see Walmart emerge at the top of the list, accounting for 39% of spoofing attempts. Microsoft topped last year's statistics but fell to second place, with 14% of attacks. LinkedIn and DHL were pushed out of the Q3 list by financial services company Wells Fargo (8%), search giant Google (4%), and Amazon's mega-ecommerce platform (4%).
Walmart
Scammers focus on brands that people trust. In North America, Walmart is a household name with millions of devoted online and brick-and-mortar customers. The high spoofing numbers associated with Walmart this year connects to several different campaigns. One rides on legitimate Walmart sweepstakes and tries to squeeze shoppers for sensitive information. Some scams offer free Walmart gift cards and then redirect shoppers to phony websites when they click on the link.
Microsoft
This platform sits at the top of the average person's technology stack. Microsoft's Outlook is among the most popular business and personal email services. Millions of people run the ubiquitous Windows operating system on both home and work devices. With so many relying on Microsoft, users will likely treat messages with trust and urgency. In earlier quarters, Microsoft topped the "most spoofed" list. Users should be wary of emails from Microsoft suggesting suspicious activity on their accounts.
Wells Fargo
This multinational financial services company boasts over 70 million customers in nearly three dozen countries. Naturally, account holders want assurance that their money is safe. Fraudsters have exploited this concern by sending emails under the Wells Fargo brand asking customers to update their accounts. When customers click, they’re sent to a fraudulent website and asked to log in. Logging in means handing over account information to the impersonators leading the scam. Customers of any known bank should watch out for similar spoofing attempts and recall that banks never ask users to share login credentials.
With so many free services under one company roof—from Gmail to Docs, Maps, Photos, Play, and more—Google is one of the most well-known brands in the online world. That proliferation of services makes Google a perfect brand for financial criminals to emulate in spoofing attempts. From Gmail notifications to messages related to Android devices and apps, fraudsters have endless avenues to reach Google customers. Many users conduct all their work and social and professional activities on Gmail, Google Photos, and Google Drive. If an email from "Google" says your account might be compromised, it's easy to panic and follow the instructions in the email without checking for red flags.
Amazon
eCommerce giant Amazon edged out delivery companies DHL and FedEx on CPR's most recent "most spoofed" list. However, as in spoofs of those companies, Amazon spoofing attempts are related to product orders and deliveries. A common Amazon scam involves scammers sending fake purchase alerts, tricking you into believing you've been charged for expensive items. The message includes a phone number for you to call. When you learn you might be charged for an item you didn't buy, you're eager to resolve the situation. Scammers rely on that eagerness in hopes people will expose passwords and other sensitive details.
What is the Most Common Type of Spoofing?
Impersonations that arrive via SMS and phone can also be considered spoofing. Phony websites also count. Even so, the most common target vector is—you guessed it—email. Spoofing by email is on the rise. GreatHorn’s 2023 State of Email Security report indicates that impersonation emails now make up 43%—nearly half—of the cyber attacks that appear in your inbox.
How to Beat a Spoofing Attack
Because some cyber attackers are so good at imitating known brands, they might be hard to detect. Keep in mind that a spoof is simply a sophisticated version of a phishing attack. The same detection methods apply and can help you sniff out a spoofing attempt every time.
- Always be cautious with unexpected notification emails.
- Quickly scan the email content for unusual language, spelling, or grammar mistakes.
- Check for inconsistencies in logos, colors, and design, which can indicate a spoof.
- Verify the domain name carefully; scammers may use look-alike domain names with subtle changes, like special characters. For instance, they might replace the letter 'l' with the number '1' in a domain, such as using "1inkedintechsupport.com" instead of "linkedin.com."
By staying vigilant and applying these simple verification steps, you can protect yourself against the cunning tactics of spoofing cyber attackers.
Hackers Will Still Spoof Brands
Spoofing is growing more commonplace and is likely to get more sophisticated, especially with AI. Impersonating a brand checks too many boxes for financially motivated hackers. Remember, these are companies that contact users on a regular basis. People are used to sharing some of their personal information to access these critical services. Imitating world-famous brands earns fraudsters instant trust and easy access to millions of people. Thankfully, the tools people need to deflect spoofing and phishing attempts are within reach. Cyber security awareness teaches the signs of spoofing and trains people to identify and report phishing attempts. Spoofing attacks fail when you take the time to scrutinize and recognize the attempt. Equip yourself and your team with the knowledge to detect and avoid these scams by learning the 7 signs of phishing emails—your first line of defense. Read our blog to further cultivate a cyber-aware culture across your organization.
Cyber Security Hub: Access Exclusive Cyber Security Content
Take advantage of our free Cyber Security Hub – it is your one-stop cyber security awareness and knowledge center with one-click access to our spoofing Kit, Work From Home Kit, Password Kit, Phishing Kit and more.