One of the most frequent attack vectors for cyber attackers is also one of the most used workplace applications.
And you guessed it... that application is email.
Thankfully, a lot of sophisticated technology these days can help protect organizations from cyber threats. Even so, this attack vector still puts your end users on the front lines of the cyber security threats.
This means that to secure your perimeter, your employees need to know the signs of a phishing email and what to do when they receive one. Read on to learn how your employees can make or break your overall cyber security.
What is a Phishing Email?
A phishing email is a sham message asking the recipient to perform some action. Commonly, the goal of this email is to obtain sensitive information to use for fraudulent purposes. A cyber attacker might also use phishing to gain access to systems, steal data, or cause other damage.
Most phishing emails seem plausible. They claim to be from trusted colleagues, business partners, or even company brass. As a result, cyber attackers deceive recipients into disclosing private information—dates of birth, social security numbers, credit card details, and even passwords to enterprise software.
These spam emails may also have attachments that launch malware and infect computers with just one click.
Why is Phishing Awareness Important?
Cyber attacks via phishing emails are not only prevalent, but they’re also constantly evolving. For organizations to protect themselves, employees should be familiar with the latest threat types to anticipate, recognize, and report them.
Unfortunately, most employees aren’t up to speed with what’s happening in cyber security. A survey conducted by Fortra’s Terranova Security in 2022 showed that only 30% of employees believe they have good knowledge of cyber security risks and that only 22% believe their colleagues show adequate awareness.
Those self-assessments are not far from reality. The Gone Phishing Tournament, run by Fortra’s Terranova Security and sponsored by Microsoft, put 250 organizations and 1.2 million employees to the test in a phishing simulation.
Sadly, 7% of participants clicked on the tournament’s simulated phishing email. Of those, 3% went further and provided the sensitive data the phony message asked for. These numbers might seem too small to worry about but remember that it only takes one click for a data breach to happen.
Therefore, organizations must eliminate these clicks. However, just telling staff that emails can be risky isn’t enough. Employees need phishing awareness training that includes hands-on practice and frequent testing to keep those lessons top of mind and up to date.
7 Common Indicators of a Phishing Attempt
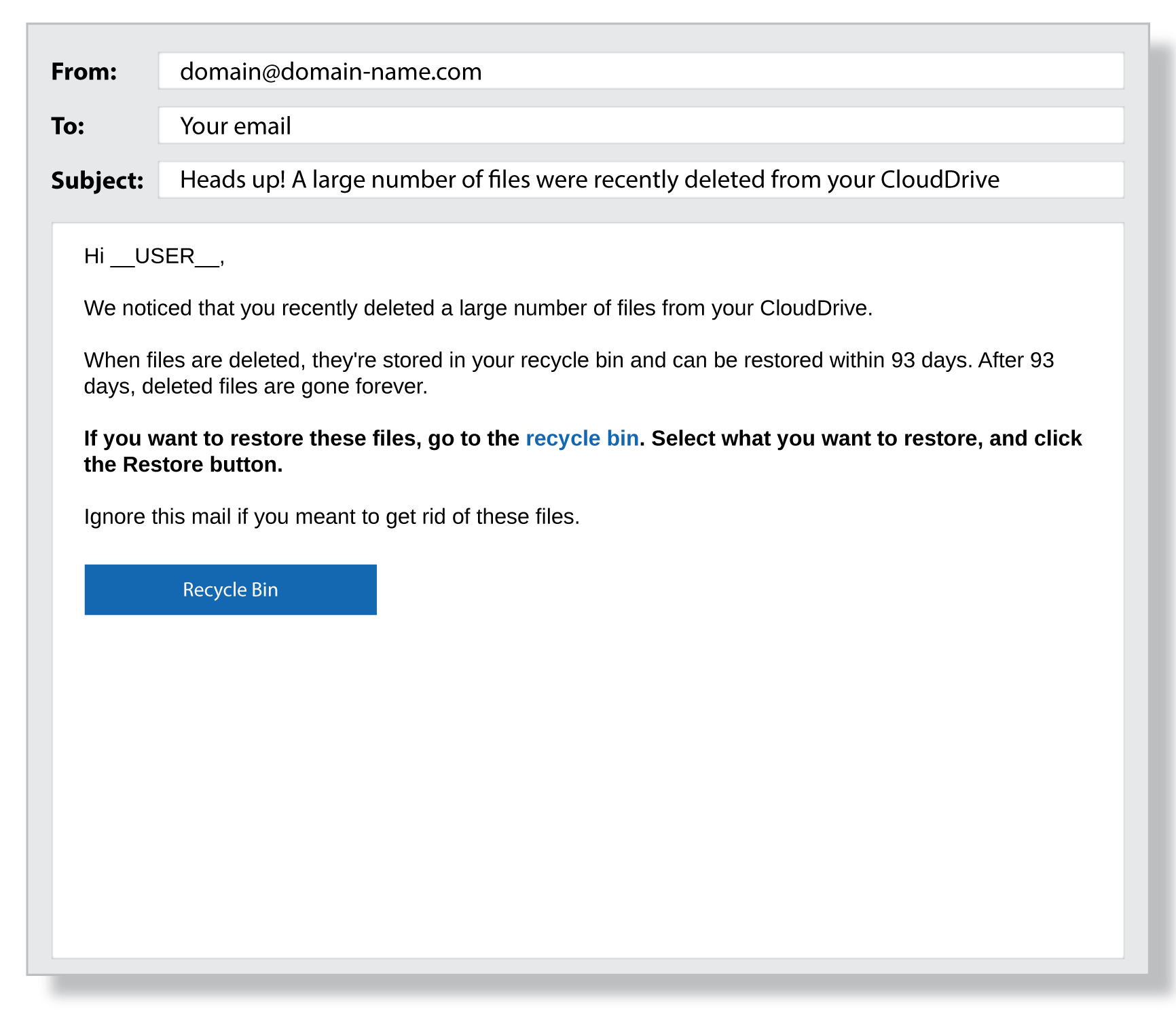 Despite the various "flavors" of phishing emails, there are commonalities. Cyber security professionals have valuable intel on what they look and sound like. Fancy some detective work? Here are 7 "clues" that you're dealing with a phishing email, not a regular email request.
Despite the various "flavors" of phishing emails, there are commonalities. Cyber security professionals have valuable intel on what they look and sound like. Fancy some detective work? Here are 7 "clues" that you're dealing with a phishing email, not a regular email request.
1. Requests for information
Phishing emails usually try to steal personal data, so any unsolicited request for this info is a telltale sign of phishing. Watch out for emails that link this data request to a fabulous prize or a missed delivery. Retailers, social media companies, and financial institutions never ask for personal information through email, so it's good to be skeptical.
2. Mismatches between emails and URLs
Phishing emails are often lookalikes, designed to appear like official communications. Their fraudulent email addresses and URLs often differ only slightly from valid ones. Compare details with previous emails to verify they're from trusted parties. Before you click any links in the message body, hover your mouse over them to see the link address and ensure they redirect to legitimate sites.
3. Unusual greetings
People use language in highly idiosyncratic ways. This characteristic is a great thing when it comes to detecting phishing emails. If a colleague or friend writes to you using unfamiliar language or a tone that doesn't "sound" like them, it's a signal to pause and scrutinize the message.
4. Typos and errors
Cyber criminals have computer skills, not proofreading skills. Emails from respected brands and professional organizations are not full of mistakes. Think twice before complying with shoddily written requests.
5. Urgent asks
The success of phishing relies on the nature of email and the nature of work. Cyber attackers know employees are busy and get dozens of emails every day. To exploit this, they add urgency to their messages or include threats like, "Act fast or lose your account access." If you feel pressured to act too quickly, it could be a phishing attempt.
6. Unusual attachments
Be wary of emails with invitations to download attached software or open files, especially if the request comes out of nowhere. Cyber attackers often use attachments to get you to install malware on company computers. Unusual file names and unfamiliar file types are red flags.
7. Low-quality graphics
While the social engineering aspects of phishing can be sophisticated, the "look" of phishing emails can give them away. Look for poorly designed and fuzzy images, stock photos, strange font choices, and unusual formatting. Be suspicious of "image-only" emails that lock text inside .jpeg or .png files—this is a favorite approach of spammers and phishing attackers.
Learning Exercise:
Take a closer look at common phishing signs in this interactive training exercise.
How to Prevent Phishing Attacks
While the types of phishing exploits are evolving and growing, so are the means you have to prevent them. Here are the best techniques for stopping a phishing attempt before it becomes a breach.
- Cyber security awareness training: Introduce a training program that teaches your employees how to detect phishing emails and recognize other common cyber attack
- Phishing simulations: Run phishing simulations to train and test your employees' ability to detect phishing emails. Give departments or individuals with shaky results some extra training.
- Phishing policy: If you get a phishing email, your colleagues might be getting the same one, too. Implement a "see something, say something" policy to raise awareness around phishing attacks and patterns affecting your organization.
- Multi-Factor Authentication: Use multi-factor authentication for system access. If an attacker succeeds in gaining an employee's password, they won't gain access without a second piece of authenticating data or technology.
- Biometric logins: Use biometric identification for system access to eliminate the opportunity for cyber attackers to steal passwords.
Shore Up Your Perimeter with Phishing Awareness
Cyber criminals use phishing emails to punch holes in your security perimeter. They know that not all employees have the knowledge or the time to detect phony messages when they pop up in their inboxes. Access through one staff member—a single set of stolen credentials—could open the floodgates to more breaches inside your organization or cause damage to upstream and downstream partners. Proper training in cyber security awareness is the best way to plug those holes. It gives employees the confidence to recognize phishing email attempts and the know-how to react in ways that protect your organization.
Remember that 7%? Are you wondering if your staff would "click"?
Get a free demo to assess the security maturity of your employees and bolster their phishing email detection capabilities with a cyber security awareness program tailored to your business.