
With roughly 5 billion people — a whopping 65% of the global population—sending and receiving SMS messages, it’s no wonder that hackers have taken to SMS as a new way to lead cyber attacks.
In 2024, 56 million Americans were impacted by phone scams. And only 65% of Americans say they would delete a text if it came from an unknown sender. With these kinds of numbers, the odds are in hackers’ favor.
These phishing attacks using SMS communication are known as smishing (for ‘SMS phishing’). The threat actor’s goal in these attacks is essentially the same as in an email phishing attack.
Hackers send links to thousands of phone numbers, urging recipients to click on a fraudulent link designed to trick them into revealing personal information or installing malware on their devices. They use different types of smishing to create fraudulent scenarios and target other platforms. Similar attacks can target messaging apps like iMessage, WhatsApp, and Facebook Messenger. These threats may also extend to platforms such as Google Chat and Microsoft Teams, putting users at risk of revealing personal information or installing malware.
Let’s look at the seven most common smishing attacks and how you can protect yourself.
7 Examples of Smishing
The delivery notification
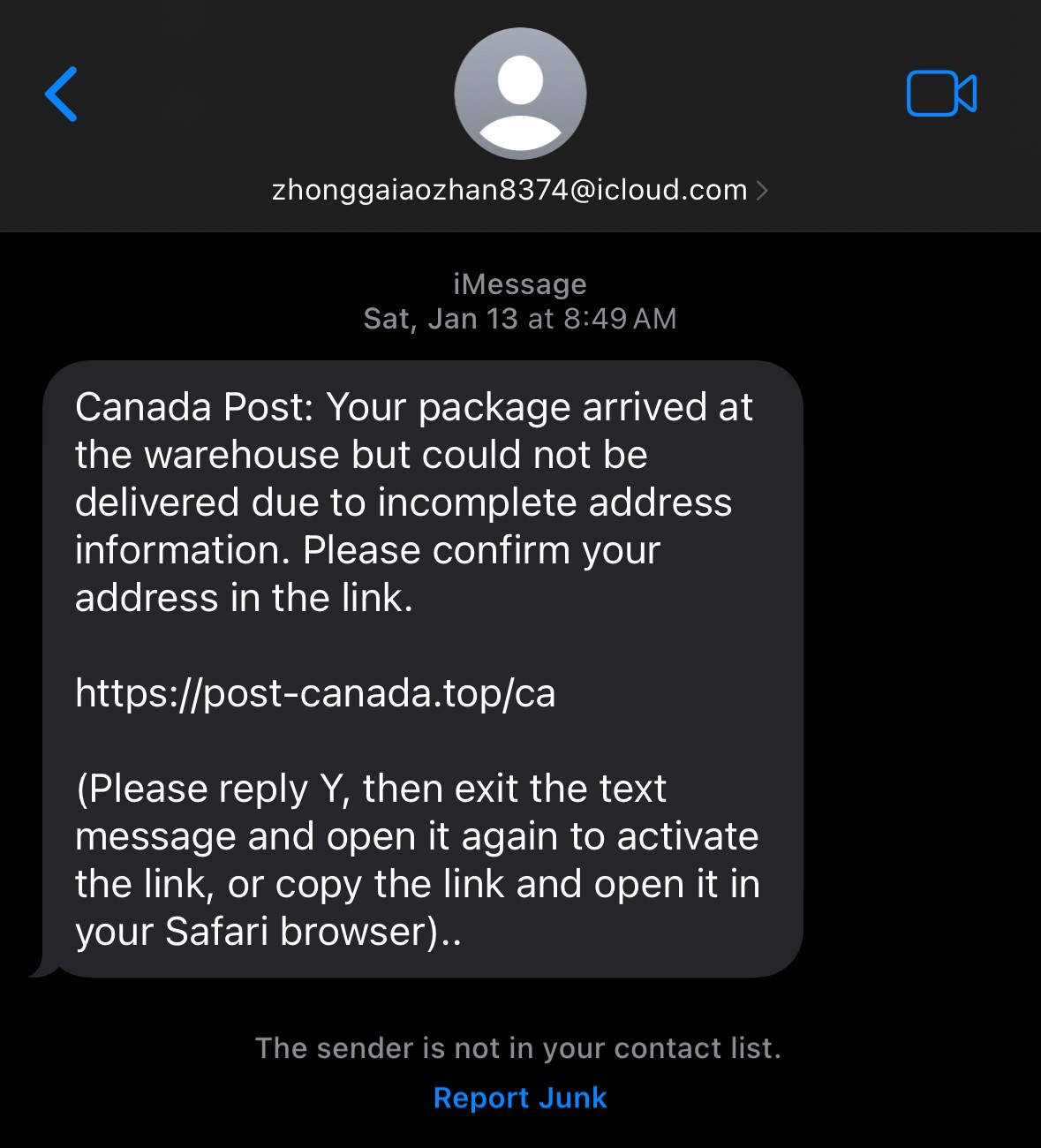
With the rise of online shopping, people are always waiting for packages and checking on the progress of their deliveries. Since many websites and delivery companies offer text message updates, most users don’t think twice when they receive a text offering a tracking link.
Some delivery companies use SMS to update their consumers, and they use links directing consumers to their domains. These scams typically use URL shorteners or have domain names that spoof legitimate ones, so always be watchful.
The bank/credit card text
Smishing attacks use financial institutions as cover because any type of notification about the interruption of funds or unpaid bills can be a stressful, urgent matter. If people think there's an issue with their bank account, they are more likely to click a link and settle it immediately.
While banks and credit card companies send text messages to their customers, they never include links. Legitimate messages from financial institutions always are simple and describe the nature of the issue in general terms. It will prompt the user to sign into their account, ensuring they access the site securely.
The raffle win
Although most people quickly dismiss these messages as spam, especially since they rarely enter raffles, those who have recently participated in a contest might be more susceptible to clicking on them, potentially leading to malware on their devices.
For these attacks, it’s important to remember that legitimate contest organizers will use email to notify winners. This makes it easy for them to communicate with you and gather the information needed to send you the prize.
The password reset
With the increase in password breaches from several well-known websites, many users have turned to two-factor authentication (2FA) to protect themselves and their information. This additional security measure has created a new scam where hackers use SMS to steal passwords.
After establishing a victim’s phone number and email address, hackers send a smishing text to the user saying their account experienced a breach. Usually, their email has been compromised. The hackers then use the “forgot my password” function on the website to send a 2FA code to the victim’s phone.
The smishing message will ask the user to give the hackers the code they received via text to secure their account. Doing so gives scammers control of the account.
Remind your users to never share their 2FA codes with anyone under any circumstances. Recommend using an authenticator app instead, as it offers a more secure and tamper-proof method of authentication.
The tax season scam
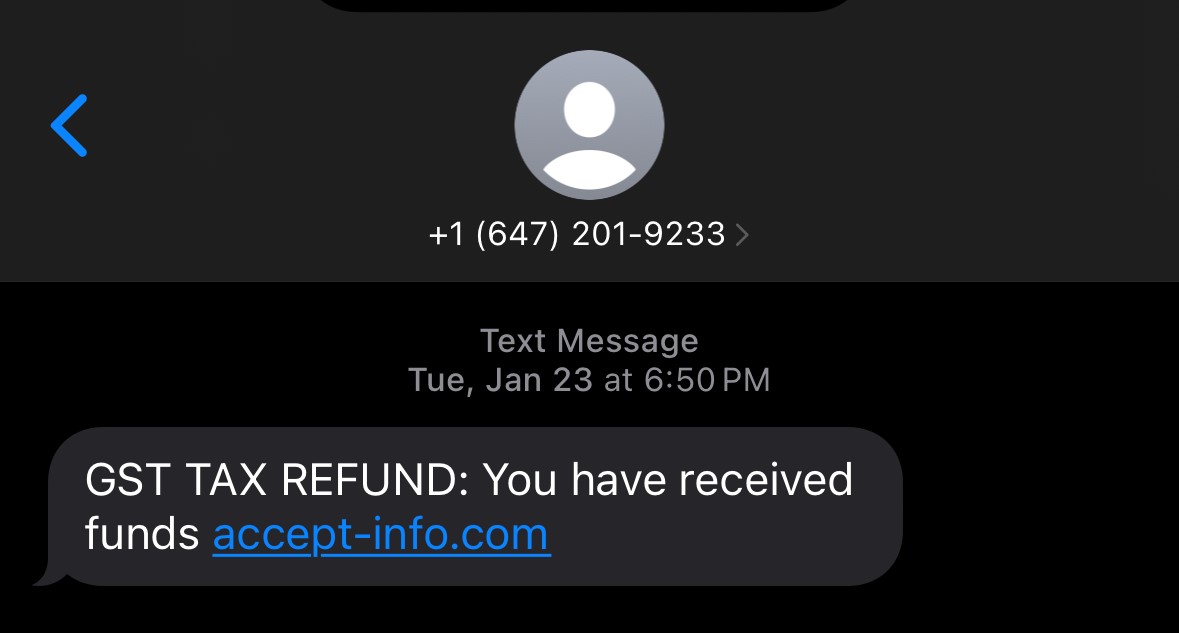
‘Tis the season to be leery. Tax season is rife with smishing scams. The most common scams try to convince their victim that they owe money after doing their taxes and direct them to a fraudulent website to pay the required amount.
Another common tactic is telling the victim they will receive a large refund, inviting them to click a link to claim their money. Doing so installs malware on their phone.
Again, remind your users that such payments and tax refunds are only paid via check or bank transfer. Additionally, tax and revenue agencies only communicate using email and physical letters, never via SMS.
CEO fraud
Everyone wants to impress their superiors at work. So, when your CEO sends you a text message asking for your urgent help, you’re bound to jump to the task. That’s the sentiment that hackers rely on using the CEO fraud technique.
Text messages in these smishing attacks will be cleverly crafted, urging the user to complete a task immediately. Often sent right before the end of the business day, they demand the information be sent before the victim leaves the office.
It’s important to remind your users that your company’s CEO will always use proper channels to contact them, such as reaching out to their direct superior. Once again, these attacks are always sent from bogus emails and rely on urgency and the fallibility of human nature to succeed.
The ridiculous message
While most scams mentioned here are clever and expertly crafted, some are just outright ridiculous on purpose. Think of the infamous Nigerian Prince scam — making outrageous claims and riddled with spelling and grammar mistakes.
Hackers use these ridiculous messages to weed out the people who wouldn’t fall for this scam. Often targeting older people who might be lonely and happy to respond to any text message they receive, these smishing attempts will often claim to be long-lost family members and ask for money to get out of the bind.
While you and your users may not be targets for this scam, your older relatives might fall prey to them. Always be on the lookout if they need to send money to an uncle you’ve never heard of or even if they mention helping a new friend.
How to Protect Yourself from Smishing
Anyone can receive a smishing text—you might be next or, more probably, you’ve already received them. You must know what to do if you become an attacker’s next target. Here are some tips to protect yourself from text scams and smishing attacks.
- Educate yourself on the risks of malicious text messages. If you are a business owner, invest in security awareness training to build a cyber-aware organizational culture.
- The best defense against smishing is to do nothing and ignore these messages. If something doesn’t feel right when you receive a text , don’t engage with it. Remember that legitimate messages from government agencies and financial institutions will come through official channels if an issue warrants your attention.
- Educate yourself and your employees about smishing tactics, social engineering attacks, and other scams. Be aware of what cybercriminals do to trick victims through text.
- Regularly monitor smishing awareness. Stress that they need to read every text they receive carefully and, when in doubt, never respond.
- Hold security awareness simulations to assess your workforce’s resilience against smishing attacks. And when necessary, conduct training through gamification and micro and nano learning modules.
- Install anti-virus software and malware protection on all mobile devices, especially for businesses with a bring-your-own-device (BYOD) policy.
- Regularly communicate with employees about smishing and hold periodical awareness campaigns.
Take Proactive Steps Against Smishing
Given the near-universal presence of SMS-capable phones, it's no surprise that hackers exploit SMS for cyber attacks. Smishing attacks, like email phishing, aim to steal confidential personal and corporate information.
The good news is that by proactively and regularly providing security awareness training, you can equip your employees with the tools to effectively respond to threats ranging from smishing attacks to ransomware and social network breaches.
Are you ready to enhance your security awareness training program? Schedule a demo with Fortra Security Awareness Training to get started.