What is a Phishing Simulation?
Phishing simulations are imitations of real-world phishing emails organizations can send to employees to test online behavior and assess knowledge levels regarding phishing attacks. The emails mirror cyber threats professionals may encounter in their daily activities, both during and outside work hours.
Fortra's
Phishing Simulation
Software
Test your employee's skills and measure their progress.
What are the Features
of the Best Phishing Simulation Software?
The best phishing simulation software balances a flexible, easy-to-use interface with realistic phishing templates that target specific behaviors and emulate common cyber threats. Terranova Security offers a wide variety of phishing simulation solutions for organizations of all sizes, industries, and regions, providing security leaders with the tools they need to ensure confidential data is kept safe from hackers.
Mirrors real-world cyber threats
Easy-to-use interface
Customizable phishing scenarios
Seamless training program integration
Data-driven performance measurement
See Phishing Simulation Software in Action
What are 4 types of phishing?
Of the hundreds of the known phishing scams that exist, here are the four most common types:
How can phishing be prevented?
Education on common cyber threats is the best way to prevent a phishing-related data breach. Implementing security awareness initiatives combined with phishing simulation training is the ideal recipe for strengthening data protection. Keeping the conversation going outside scheduled training periods will also help keep your employees alert and aware of all phishing-related scams they may encounter.
For more insight on ways to strengthen your phishing prevention strategy, visit the dedicated Terranova Security cyberpedia page: What is Phishing?
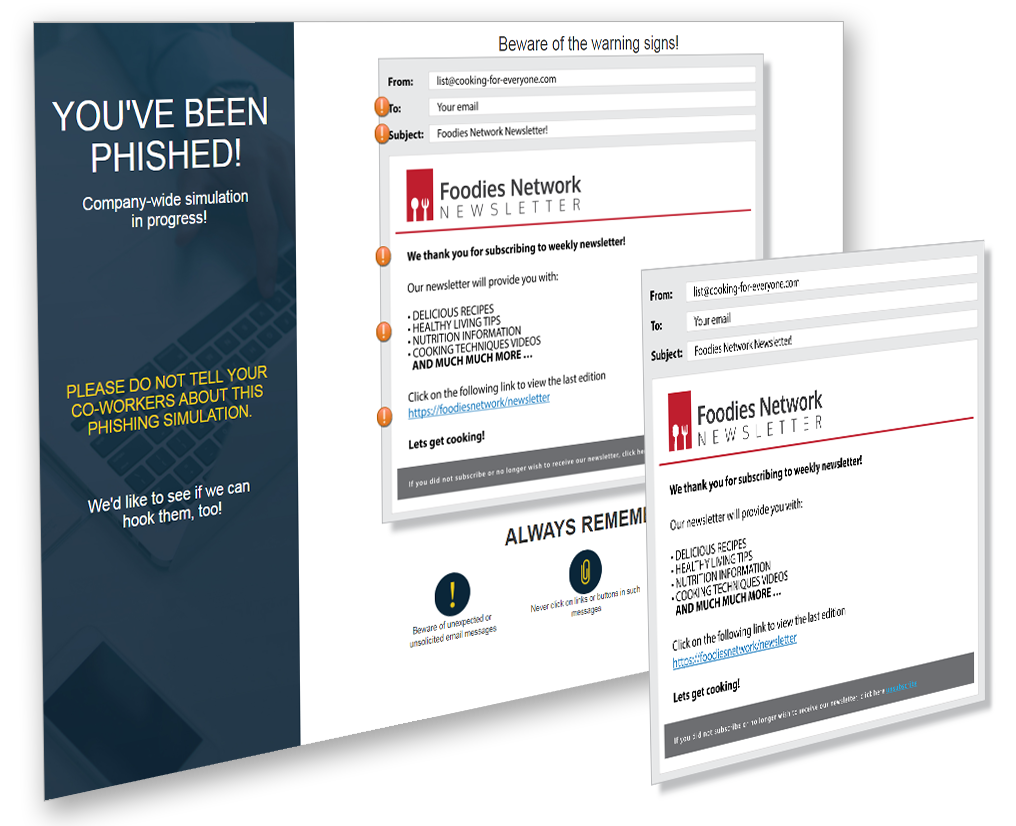
 From fraudulent shipping confirmation messages to suspicious gift card and refund offers, Fortra Security phishing templates replicate real-life attacks that can occur at any time.
From fraudulent shipping confirmation messages to suspicious gift card and refund offers, Fortra Security phishing templates replicate real-life attacks that can occur at any time. Fortra Human Risk Management makes creating, deploying, and monitoring simulated threat scenarios simple from start to finish.
Fortra Human Risk Management makes creating, deploying, and monitoring simulated threat scenarios simple from start to finish. Administrators can customize any aspect of selected Fortra phishing scenarios, from the phishing email message to the CSS styling of the fake landing page.
Administrators can customize any aspect of selected Fortra phishing scenarios, from the phishing email message to the CSS styling of the fake landing page. No matter what kind of security awareness program you have or are looking to implement, you’ll find templates that align with your existing training topics and cyber security goals.
No matter what kind of security awareness program you have or are looking to implement, you’ll find templates that align with your existing training topics and cyber security goals. Make informed, data-driven decisions regarding your phishing awareness strategy with in-depth analytics and reporting capabilities.
Make informed, data-driven decisions regarding your phishing awareness strategy with in-depth analytics and reporting capabilities.

